Updated – 27/07/2021 – Update Rollup 2 for Microsoft Azure Backup Server v3 is released.
Updated – 25/06/2020 – Update Rollup 1 for Microsoft Azure Backup Server v3 is released.
Updated – 09/09/2019 – Azure Backup Server v3 now supports Windows Server 2019 workloads for protection.
In this article, we will show you how to install Microsoft Azure Backup Server (MABS) v3.
Table of Contents
Introduction
In October 2015, Microsoft released the first version of Microsoft Azure Backup Server MABS v1 (known as project VENUS). And last year, in May 2017, Microsoft released the second version of Microsoft Azure Backup Server MABS v2.
The user’s voice was very active in the previous months. Many users, including myself, were requesting if MABS will be updated to support the latest features and enhancements introduced in SC DPM Semi-Annual Channel (SAC) versions 1801 and 1807.
Microsoft is listening to us, and they released the third version of Microsoft Azure Backup Server (MABS v3).
As I mentioned in my previous article, Microsoft Azure Backup Server (MABS) inherits the same functionality as System Center Data Protection Manager (SC DPM) for workload backup, if you are familiar with SC DPM, MABS looks very similar. However, MABS does not support tapes nor can integrate with any System Center component, so if you need System Center integration, you need the full SC DPM license.
The good news is, that MABS comes with a free SQL Server license that can only be used for the MABS database, and it is free to download. Did I say free? Yes, it’s FREE! I believe the vast majority of customers will choose Microsoft Azure Backup Server (MABS), and save on System Center licensing costs.
With Microsoft Azure Backup Server v3, you can protect application workloads such as Hyper-V VMs, Microsoft SQL Server, SharePoint Server, Microsoft Exchange, VMware VMs, and Windows clients to:
- Disk (D2D), giving high Recovery Time Objectives (RTOs) for tier 1 workloads, and short-term protection on-premises.
- Azure (D2D2C) for long-term online and off-site protection. (Backup to Tape is NOT supported).
On September 9th, 2019, Microsoft announced that Azure Backup Server V3 now supports Windows Server 2019 workloads for protection as well. To see the entire support matrix for Azure Backup Server, please check the following document.
What’s New in Azure Backup Server V3
MABS v3 has the same functionality as MABS v2 in addition to the following enhancements which were also introduced in DPM 2016 UR5 & DPM 2016 UR6, DPM 1801, and DPM 1807:
1) SQL Server 2017 as MABS database: MABS v3 can be installed with SQL 2017. You can either upgrade your SQL server from SQL 2016 to SQL 2017 or you can use a fresh instance of SQL 2017. With MABS v3 you can seamlessly back up Microsoft SQL Server 2017 workload.
2) Transport Layer Security (TLS) protocol version 1.2 support. For MABS v3, TLS 1.2 is applicable for protecting workloads in the cloud.
3) Backup Storage Migration is similar to SC DPM 2016 with Update Rollup 4.
4) Prevent unexpected data loss: With MABS v3 you can disable volume(s) from being used as target storage using PowerShell similar to SC DPM 2016 with Update Rollup 4. All volumes and mount points, except System Volumes, are available for MABS storage.
5) VMware Backup (VMware VM Backup was not supported in a production environment with MABS V2). With MABS v3, it’s supported in the production environment.
6) Optimized Consistency Check (CC) for Hyper-V VMs with RCT: MABS v3 optimizes network and storage consumption by transferring only the changed data during any CC for RCT VMs, the native change tracking starting with Windows Server 2016 Hyper-V onward.
7) Custom Size Allocation: With MABS v3 you can configure the storage to accept the default volume size, instead of calculating the size of each file and folder being backed up.
Prepare Azure Backup Server V3 Installation
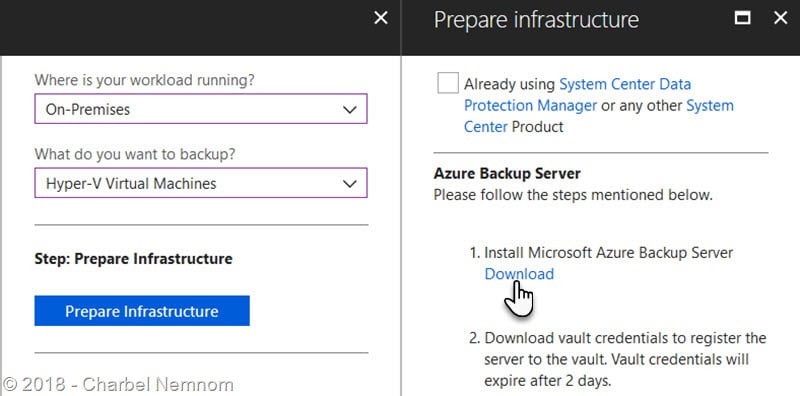
You can download MABS v3 directly from here (4.2 GB), or you can download it from the Azure Portal under Recovery Services Vault | Backup | Prepare Infrastructure as shown in the following screenshot:
Next, you need to download the vault credentials file, which is a certificate generated by the Azure portal and valid only for 2 days. From the Azure Portal, open your Recovery Services Vault and browse to the Settings section.
Under Properties, click on Backup Credentials, select Already using the latest Recovery Services Agent, and click the Download button. Make sure that the vault credentials file is saved on your MABS Server because we will use it in a subsequent step.

Install Azure Backup Server V3 on Windows Server 2019 and SQL Server 2017
The installation of MABS is straightforward, you can check my previous article on how to Install Microsoft Azure Backup Server V2 on Windows Server 2016 and SQL Server 2016 using the graphical user interface (GUI).
In this article, I will show you how to automate the installation of Microsoft Azure Backup Server (MABS V3) and SQL Server 2017 on top of Windows Server 2019. The same steps will also apply to Windows Server 2016.
Automate SQL Server 2017 Installation
Please note that Microsoft Azure Backup Server supports only local machine SQL Instance, remote SQL instance is not supported. As mentioned earlier, SQL Server 2017 shipped for free along with MABS v3, it’s the recommended version.
Open the command prompt window as Administrator, then navigate to the SQLSVR2017 path located within Microsoft Azure Backup Server v3 extracted media, and run the following command on a single line:
Make sure to update the domain name, SQL service accounts and passwords according to your environment.
Setup.exe /Q /ACTION=install /IACCEPTSQLSERVERLICENSETERMS /FEATURES=SQLEngine /INSTANCENAME=MABSV3DB
/INSTANCEDIR="D:\Program Files\Microsoft SQL Server" /INSTALLSHAREDWOWDIR="D:\Program Files (x86)\Microsoft SQL Server"
/INSTALLSHAREDDIR="D:\Program Files\Microsoft SQL Server" /SQLSVCACCOUNT="VIRT\sqldpm" /SQLSYSADMINACCOUNTS="VIRT\sqldpm"
/SQLSVCPASSWORD="dpm2016+1" /AGTSVCACCOUNT="NT AUTHORITY\Network Service" /SECURITYMODE=SQL
/SAPWD="dpm2016+1" /SQLTEMPDBDIR="D:\Program Files\Microsoft SQL Server\TempDB\\"
/SQLUSERDBDIR="D:\Program Files\Microsoft SQL Server\SQLData\\" /SQLUSERDBLOGDIR="D:\Program Files\Microsoft SQL Server\SQLLog\\"After a short period of time, the installation will be complete as shown in the screenshot below:

Starting from SQL 2016 onward, SQL Server Reporting Services (SSRS) and SQL Server Management Studio (SSMS) are now packaged and installed separately with only a web link to each download page within the SQL Server Installation Center. The good news is, Microsoft has included both installation packages in the same SQLSVR2017 folder.
Within the same command prompt window, type the following command to install SQL Server Management Studio (SSMS) in silent mode:
SSMS-Setup-ENU.exe /install /quiet /norestart /log log.txtWithin the same command prompt window as well, type the following command to install SQL Server Reporting Services (SSRS) as Developer free edition in silent mode:
SQLServerReportingServices.exe /quiet /InstallFolder="D:\Program Files\Microsoft SQL Server Reporting Services" /norestart /IAcceptLicenseTerms /Edition=DevOnce you install both packages, open SQL Server Management Studio (SSMS) and verify you can connect to the SQL instance name that you specified in the previous step.

Now there is an important point to consider before you proceed with MABS installation, and this step is applicable only if you install SQL Server separately and not through the MABS UI. There is a missing security login account that you want to add to SQL server otherwise the installation will fail with error ID: 811 stating “The DPM database was not created“.
This is because when you install MABS through the UI, you have two options, either you can Install a new instance of SQL Server or Use an exiting instance of SQL server, which actually add the required security account as part of SQL install through MABS.
If you are following the automated installation as documented in this article, then make sure to create a new security login in SQL Server Management Studio (SSMS) with the login name: BUILTIN\Administrators and select sysadmin under Server Roles.

Automate MABS V3 installation
MABS supports Item-Level Recovery (ILR), which allows you to do granular recovery of files, folders, volumes, and virtual hard disks (VHDXs) from a host-level backup of Hyper-V virtual machines. Therefore, the Hyper-V Role and PowerShell Management Tools features are required to be installed on Microsoft Azure Backup Server.
Open an elevated command-line window, type the following command, and then restart the MABS server:
dism.exe /Online /Enable-feature /All /FeatureName:Microsoft-Hyper-V /FeatureName:Microsoft-Hyper-V-Management-PowerShell /quiet /norestartOpen Notepad and copy the following code and save it on the MABS Server (i.e. MABSV3Setup.ini).
When creating the MABSV3Setup.ini file, please make sure to replace the text inside < > with values based on your own environment.
[OPTIONS]
UserName=administrator
CompanyName=<Microsoft Corporation>
SQLMachineName=localhost
SQLInstanceName=<SQL instance name>
SQLMachineUserName=administrator
SQLMachinePassword=<admin password>
SQLMachineDomainName=<machine domain>
ReportingMachineName=localhost
ReportingInstanceName=<reporting instance name>
SqlAccountPassword=<admin password>
VaultCredentialFilePath=<vault credential full path and complete name>
SecurityPassphrase=<passphrase>
PassphraseSaveLocation=<passphrase save location>
UseExistingSQL=<1/0 use or do not use existing SQL>Here is an example of the MABSV3Setup.ini file ready to deploy.

After saving the file, open an elevated command prompt window and type the following:
Start /wait .\Setup.exe /i /f D:\MABSV3Setup.ini /l D:\MABSv3Log.txtSit back and get a cup of coffee… After approximately 15 minutes, MABS v3 will be installed automatically as shown in the following screenshot!

Last but not least, switch to the Azure Portal and verify your MABS management server is registered with Azure Recovery Services Vault.

Update Rollup 1 for MABS V3
In June 2020, the Azure Backup team announced the Update Rollup 1 (UR1) for Microsoft Azure Backup Server v3. UR1 for MABS v3 brings exciting new updates. This update needs to be installed on top of MABS v3 RTM as described in this article.
Please note that you should upgrade to the latest Microsoft Azure Recovery Services (MARS) agent on your existing MABS v3 server. If the latest agent is not installed, online backups might fail, and no backup from the MABS server to Microsoft Azure operation will work.
Note: A fresh installation of the Update Rollup agent may require a restart of the protected server.
Here are the key new features for MABS v3 UR1:
Offline Backup using Azure Data Box (in preview)
Up until MABS v3 RTM, the initial full backups for transferring large amounts of data to Azure which require more network bandwidth and time was based only on the Azure Import/Export service.
Azure Import/Export service is used to securely import large amounts of data to Azure Blob storage and Azure Files by shipping disk drives to an Azure datacenter. This service can also be used to transfer data from Azure Blob storage to disk drives and ship it to your on-premises sites. Data from one or more disk drives can be imported either to Azure Blob storage or Azure Files. With the Azure Import/Export service, you need to supply your own disk drives which should be supported using a certain list of disks required by Microsoft.
With MABS v3 UR1, Microsoft is adding support for Azure Data Box for offline/initial seeding besides the Azure Import/Export service. With Azure Data Box you can use a Microsoft-provided disk and save on the time and cost of acquiring your own disk.

To learn more about Azure Data Box Disk, please check the official documentation from Microsoft.
First party backup solution for Azure VMware Solution
Microsoft recently announced Azure VMware Solution (AVS) which empowers customers to seamlessly extend or completely migrate their existing on-premises VMware applications to Azure. AVS customers can now use MABS v3 UR1 to protect virtual machines deployed in Azure VMware Solution. This is currently in preview and supports VM-level backup. You can read more about the steps to deploy and protect AVS virtual machines using MABS v3 UR1 here.
Faster backups with tiered storage using SSDs
With MABS v3 UR1, Microsoft has made enhancements in the backup process which can take advantage of tiered storage to deliver 50-70% faster backups. By using a small percentage (4% of overall storage) of SSD as a tiered volume in combination with HDD storage, customers can achieve higher scale and better performance.
Moving forward, Microsoft recommends using a small percentage of SSD storage (~2% to 5%) as a minimum for tiered volume in combination with HDD storage to improve ReFS cloning performance, thus results in better backup with Modern Backup Storage. The same recommendation applies to MABS v3 UR1.
Please check the following article to learn more about SSD tiered storage for faster backup.
Faster VMware backup
Using MABS you can protect VMware virtual machines. You need to configure a protection group that gathers multiple VMs and applies the same data retention and backup settings to all VMs in the group. All your VMWare VM backup jobs within a single protection group would run in parallel, leading to 25% faster VM backups.
With earlier versions of MABS, VMware parallel backups were performed only across protection groups. With MABS v3 UR1, VMware delta replication jobs run in parallel which leads to faster VM backups.
By default jobs to run in parallel are set to 8, you can modify the number using the registry key as below. Please note that the key is not present by default, you need to add it.
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Data Protection Manager\Configuration\MaxParallelIncrementalJobsIf you set the value to 1, this will run the replication jobs serially. However, when increasing the number to a higher value, VMware performance needs to be taken into consideration. Considering the number of resources in use and additional usage required on the VMware vSphere server should be the criteria for determining the number of delta replication jobs to run in parallel.
Support for protection of ReFS Volumes (with deduplication enabled)
Resilient File System (ReFS) on Windows Server maximizes data availability, scales efficiently to large data sets for workloads such as SQL Server, and provides data integrity through resiliency to corruption. With this update, you can now use MABS v3 UR1 to protect the ReFS volumes (with deduplication enabled) and workloads (Windows Server, SQL Server, Exchange, and SharePoint) deployed on the ReFS volume.
Support for an additional layer of authentication to delete online backup
Starting with MABS v3 UR1, when you try to Stop the protection of member server with Delete protected data | Delete storage online, you will be prompted to enter a security PIN as shown in the screenshot below.
Next, you need to generate the security PIN from the Azure Portal under the Recovery Services Vault which is available for 5 minutes only. So even if your MABS v3 server gets compromised, the attacker won’t be able to wipe your online data in Azure, so better safe than sorry!

Download MABS V3 UR1
You can obtain and install the update package from Windows Update directly, or using Windows Server Update Services (WSUS), or you can directly download the Update Rollup 1 from here.
Please check the official Knowledge Base article for details about these fixes and installation instructions.
Update Rollup 2 for MABS V3
In July 2021, the Azure Backup team announced the Update Rollup 2 (UR2) for Microsoft Azure Backup Server v3. UR2 for MABS v3 brings exciting new updates. This update needs to be installed on top of MABS v3 RTM as described in this article.
Please note that you should upgrade to the latest Microsoft Azure Recovery Services (MARS) agent on your existing MABS v3 server. If the latest agent is not installed, online backups might fail, and no backup from the MABS server to Microsoft Azure operation will work.
Note: A fresh installation of the Update Rollup agent may require a restart of the protected server.
Here are the latest new features announced for MABS v3 UR2:
Support for Azure Stack HCI
The good news is, with MABS v3 UR2, you can now back up Virtual Machines running on Azure Stack HCI OS.
Azure Stack HCI is a new hyper-converged infrastructure (HCI) operating system delivered as an Azure service that provides the latest security, performance, and feature updates.
Support for VMware 7.0
With MABS v3 UR2, you can also back up VMware 7.0 VMs.
Support for SQL Server Failover Cluster Instance (FCI) using Cluster Shared Volume (CSV)
MABS v3 UR2 supports SQL Server Failover Cluster Instance (FCI) using Cluster Shared Volume (CSV). With CSV, the management of your SQL Server Instance is simplified. This helps you to manage the underlying storage from any node as there is an abstraction to which node owns the disk.
Optimized Volume Migration
MABS v3 UR2 supports optimized volume migration. The optimized volume migration allows you to move data sources to the new volume much faster. The enhanced migration process migrates only the active backup copy (Active Replica) to the new volume. All new recovery points are created on the new volume while existing recovery points are maintained on the existing volume and are purged based on the retention policy.
Offline Backup using Azure Data Box (in production)
MABS v3 UR2 supports Offline backup using Azure Data Box. With Microsoft Azure Data Box integration, you can overcome the challenge of moving terabytes of backup data from on-premises to Azure storage.
Azure Data Box saves the effort required to procure your own Azure-compatible disks and connectors or to provide temporary storage as a staging location. Microsoft also handles the end-to-end transfer logistics, which you can track through the Azure Portal.
Download MABS V3 UR2
You can obtain and install the update package from Windows Update directly, or using Windows Server Update Services (WSUS), or you can directly download the Update Rollup 2 from here.
Please check the official Knowledge Base article for details about these fixes and installation instructions.
Upgrade From MABS V2 to MABS V3
If you already have MABS V2 installed in your environment and you want to upgrade to MABS V3 which I highly recommend doing, then make sure to follow the procedure documented by Microsoft here.
Please note that MABS V2 is not a prerequisite for installing MABS V3. However, you can upgrade to MABS V3 only from MABS V2.
Summary
Microsoft Azure Backup Server extends on-premises data protection by using Azure as an off-site location while reducing backup infrastructure costs to maintain.
The integration between Azure Backup Server and Azure helps prevent your backups from being attacked by Ransomware and other malicious corruptions and deletions. So when the attacker is trying to delete backup data from your server on-premises, in that case, it will be prompted to enter a security PIN. Now the hacker might not have access to your server, but to get the security PIN, it needs to be able to access the Recovery Services Vault in Azure and then get the PIN to delete the Backup.
If a malicious user had access to the Recovery Services Vault and deleted your backups, there’s no need to worry though, because Azure Backup retains these backups for up to 14 days so you can recover this data. This way you can protect your backups and always ensure you have multiple recovery points to recover from, in case your server is attacked by Ransomware or otherwise. Better safe than sorry!
I hope this article is helpful to you.
Make sure to order my recent Microsoft System Center Data Protection Manager Cookbook for in-depth details about data protection and hybrid backup!
__
Thank you for reading my blog.
If you have any questions or feedback, please leave a comment.
-Charbel Nemnom-

I’m still stuck to this error when Installing and Adding Agents.
“The provided domain credentials do not have administrator access to the following items: ____. (ID: 33220)”
I wonder if there’s a group to add my domain account in order to Install/Add Agent.
Hello Lew, thanks for the update here.
Please make sure the domain account that you are using to install the MABS server, is a member of the local administrator group on the machine.
What about if you install the agent manually and then attach it to MABS/DPM as described in this article?
Hope it helps!